Three ways in. One graph.
Native connectors for your security stack. Full Cypher API for your pipelines. MCP for AI agents. Pick whichever fits — or use all three.
Already in your security stack
Install from the marketplace. Authenticate. Whisper intelligence flows into your existing workflows — no custom code required.
| Platform | Status |
|---|---|
| SplunkReal-time infrastructure enrichment inside Splunk. Install from Splunkbase. | Shipped |
| Microsoft SentinelNative connector for Azure Sentinel. SaaS transactable via Azure Marketplace. | Shipping now |
| OpenCTIInfrastructure intelligence as STIX observables inside OpenCTI. | Early Q2 2026 |
| Cortex XSOARAutomate infrastructure investigation playbooks with Whisper data inside XSOAR. | Early Q2 2026 |
More connectors in development. Using a platform we don’t support yet? Request a connector →
POST https://graph.whisper.security/api/query Authorization: Bearer sk_live_... { "query": "MATCH (h:HOSTNAME { name: $domain }) -[:RESOLVES_TO]->(ip:IPV4) -[:BELONGS_TO]->(asn:ASN) RETURN h, ip, asn", "params": { "domain": "suspicious-domain.xyz" } }
{ "data": [ { "h.name": "suspicious-domain.xyz", "ip.name": "185.234.xx.xx", "ip.threatScore": 87, "asn.name": "AS399629", "asn.org": "BL Networks" } ], "meta": { "nodes": 3, "edges": 2, "ms": 0.3 } }
Full Cypher access. Any query. Any depth.
Write any Cypher query against WhisperGraph and get structured JSON back in under a millisecond. Parameterized queries, full schema introspection, and built-in procedures like explain() and whisper.history() — everything you need to build intelligence into your own pipelines.
API capabilities
- →Cypher queries — Full graph traversal with parameterized inputs
- →Built-in procedures — explain() for threat assessment, whisper.history() for historical data
- →Graph schema introspection — Discover entity types and relationships programmatically
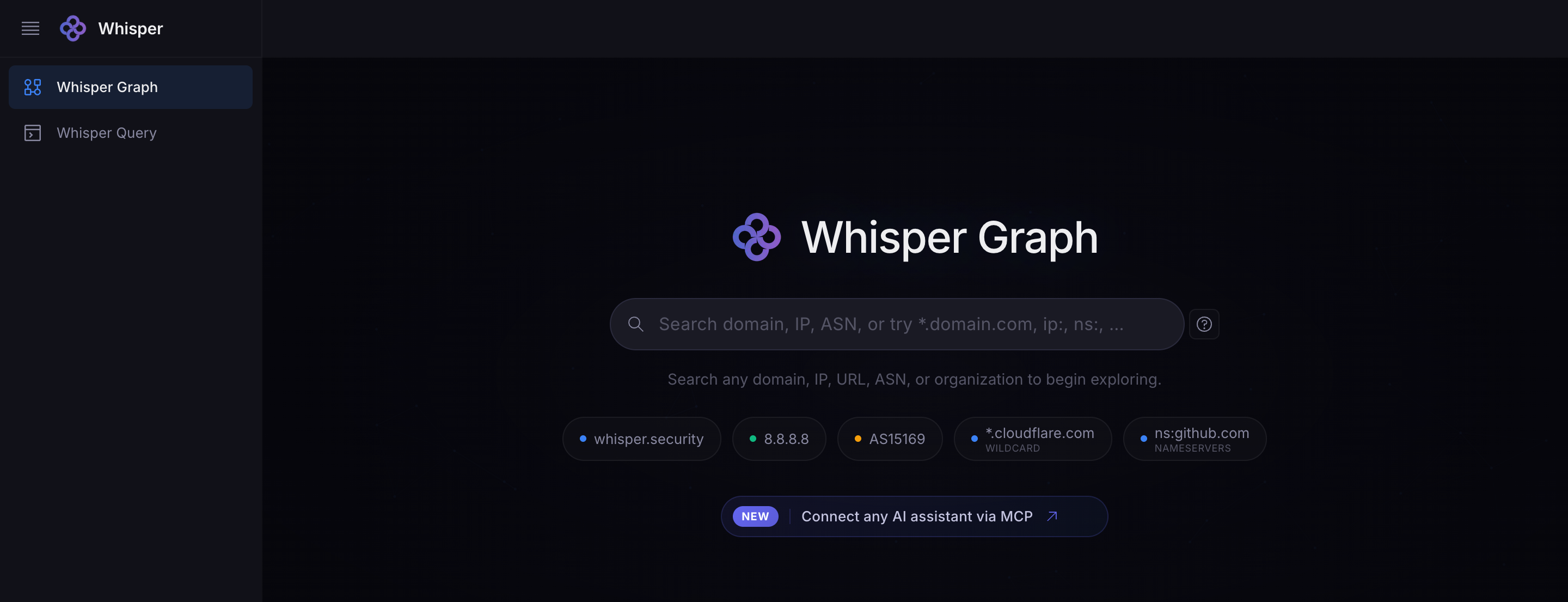
Prefer a visual interface?
Open the Console to explore the graph interactively — search domains, run queries, visualize relationships, and export results.
Open the Console →Give any AI agent internet intelligence
Connect your AI tools to WhisperGraph via MCP (Model Context Protocol). Your AI agent gets real-time access to internet infrastructure data — domains, IPs, certificates, hosting relationships — as live context, not stale training data.
$ claude mcp add \ --transport http \ whisper-graph \ https://mcp.whisper.security
We’re actively building AI Context into a full service — structured graph context for any LLM workflow, not just MCP. If you’re building AI-powered security tools, we’d love to talk.
Works with
185.234.xx.xx resolves to 14 domains, 9 of which have threat scores above 70.
The IP belongs to AS399629 (BL Networks), which hosts 1,247 other IPs. Cross-referencing shows 6 domains sharing infrastructure patterns consistent with the same campaign…
Based on live WhisperGraph data
Connect Whisper to your stack
Install a connector, query the API, or connect your AI agent. Start in under a minute.
Need help with enterprise access? Book a demo