One graph. Every connection on the internet.
Search any domain, IP, or network. See every connection — who owns it, what it hosts, how it routes, and how it changed in real time. Query instantly from your console, your SIEM, or your AI agent.
The platform
What you see when you query Whisper
Every query returns the full picture — not just the indicator, but everything connected to it, how it changed, and what it means.
Every IP, domain, certificate, ASN, and network on the internet. Ask about any one of them and see what it connects to.
Hosting, DNS resolution, routing, certificate chains, ownership, registration patterns. Not isolated data points — a connected graph you can traverse.
Fast enough for real-time alert enrichment, automated workflows, and AI agents that need answers mid-investigation.
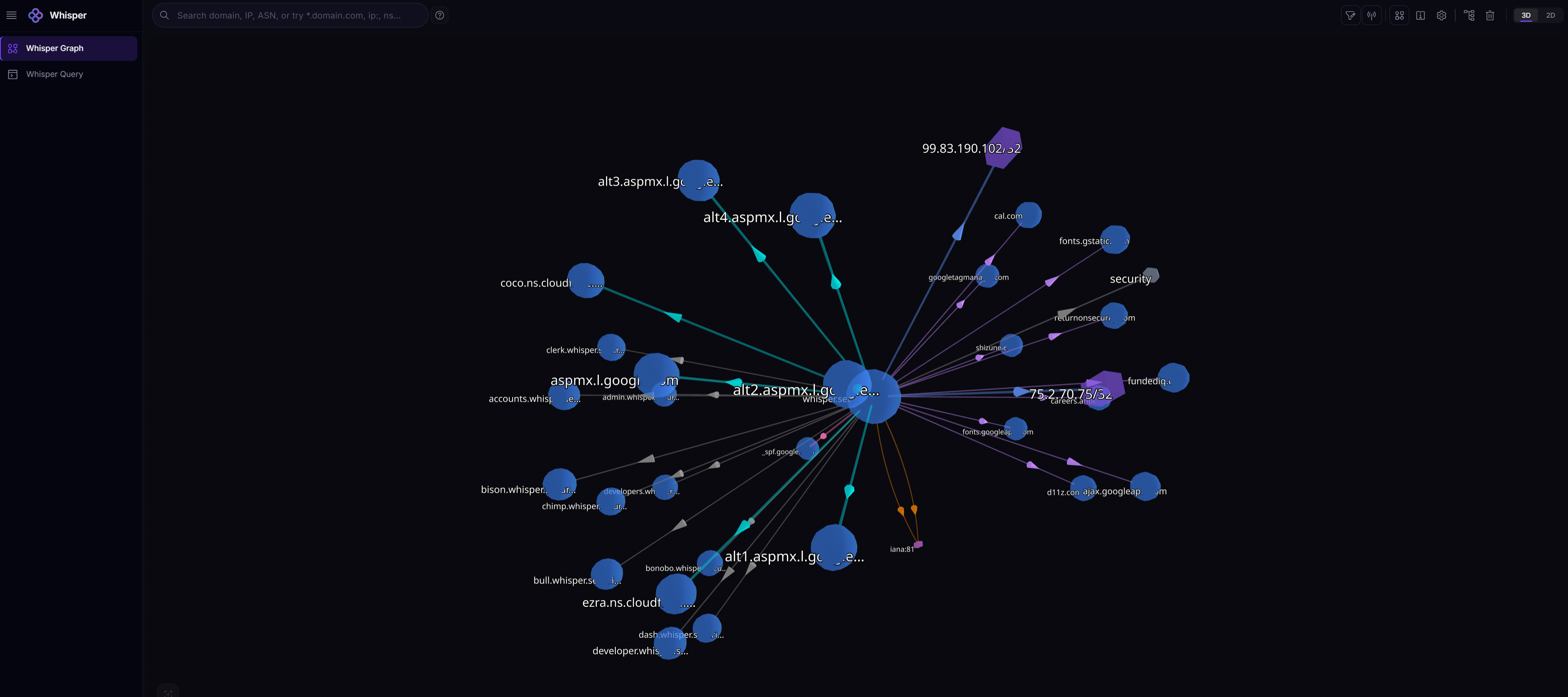
Graph Explorer
Try it yourself
Search any domain, IP, or ASN. See every connection — hosting, DNS, certificates, routing, ownership. Click any node to expand. The graph is live.
Under the hood
How the intelligence works
Three engines run continuously on the graph. Each solves a different part of the intelligence problem.
WhisperGraph™
Relationship MappingMaps every connection between internet resources into a single traversable knowledge graph. When you query an IP, you don’t just get the IP — you get every domain it hosts, every certificate it serves, every ASN it belongs to, and every other resource connected to those. Five to six levels deep, where competitors stop at two or three.
WhisperRank™
Risk ScoringEvaluates every internet resource using a dual scoring model rooted in information theory. The individual score considers blacklist history, ownership changes, domain age, and certificate patterns. The structural score evaluates the health of the network neighborhood — what else lives on that ASN, how the surrounding infrastructure behaves.
Combining both predicts risk for new domains based on organizational reputation, even if the domain itself has zero history. Every score includes a chain of evidence — you can see exactly why something was flagged.
WhisperUpdate™
Real-Time MonitoringContinuously monitors infrastructure changes as they happen. DNS changes, certificate rotations, ownership transfers, BGP routing anomalies — detected in real time via streaming connections to sources like RIPE RIS, certificate transparency logs, and zone file updates across 190+ countries.
This is how Whisper sees attack infrastructure forming before it goes live. Attackers register domains, provision certificates, configure hosting. The graph detects these pieces connecting 1-3 days before the attack.
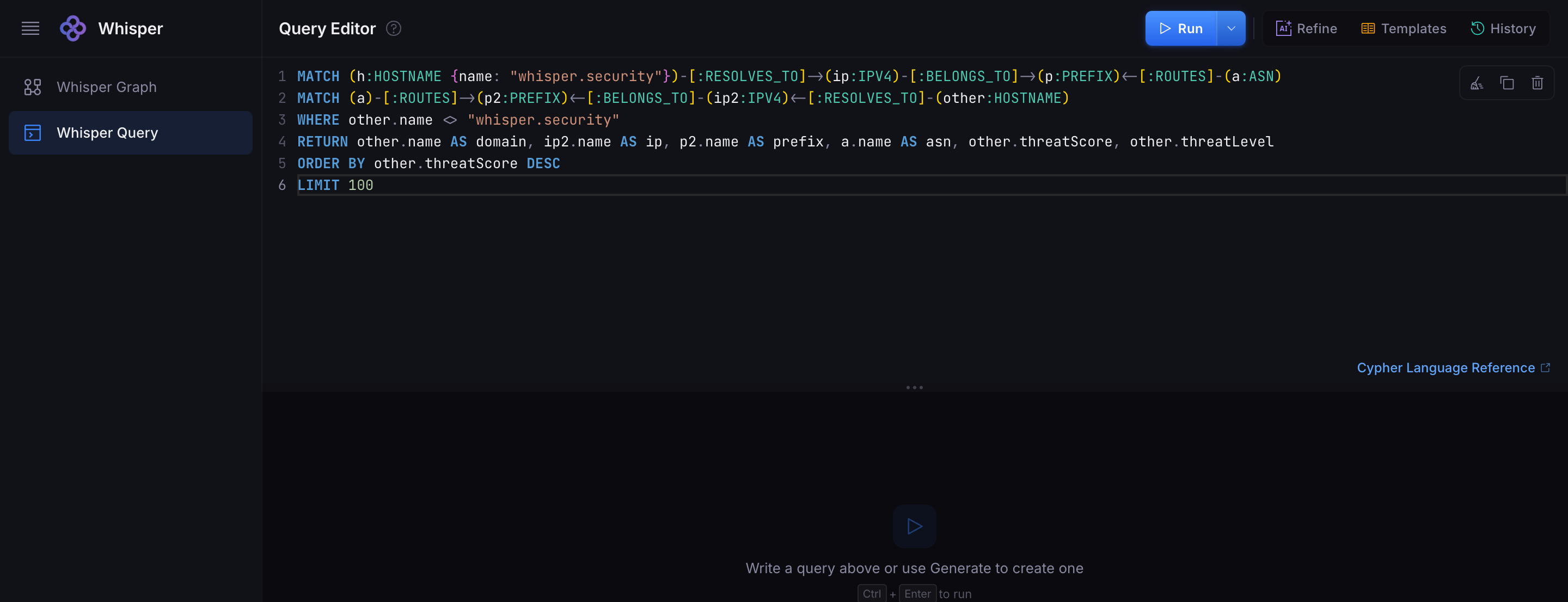
Query Studio
Ask in plain English. Or write Cypher.
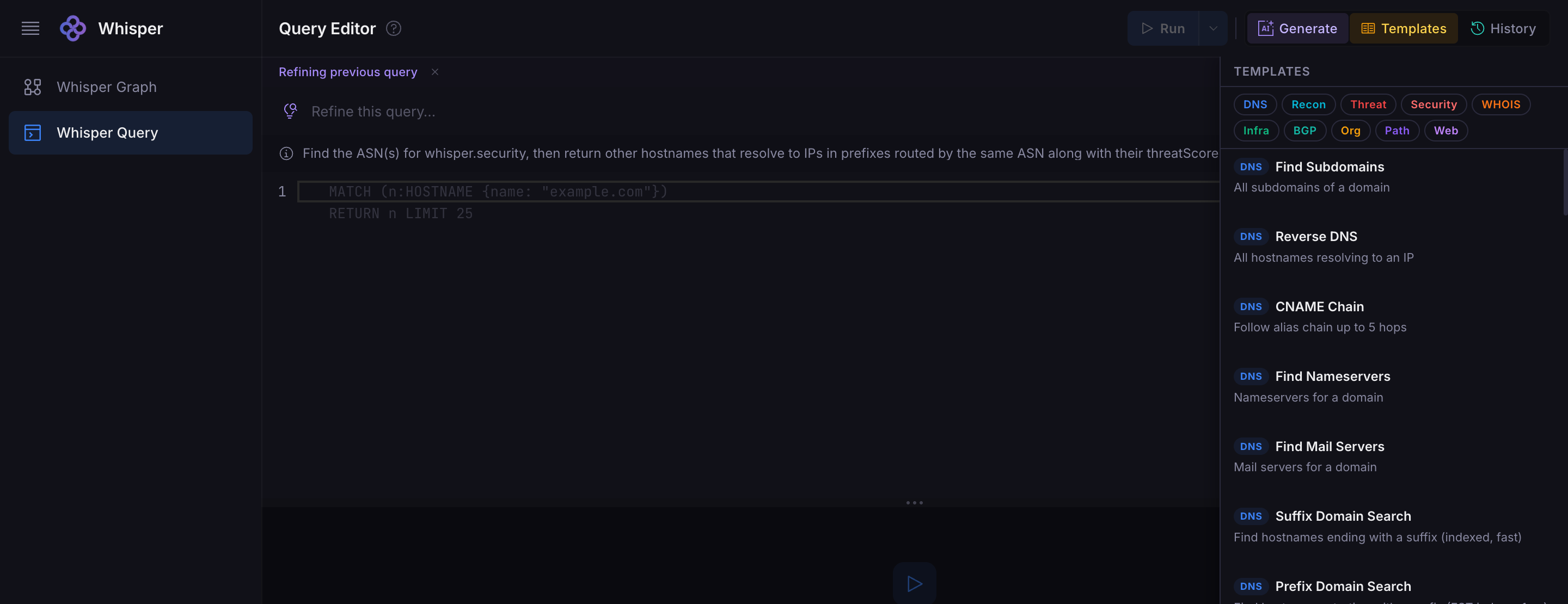
Or start from a template.
Describe what you need in natural language. The AI generates a Cypher query, validates it against the graph schema, and runs it — all in the browser. Or write Cypher directly if you prefer. Choose from pre-built templates for common investigations.
Natural Language
Describe what you need. AI generates the Cypher.
Cypher Editor
Full syntax highlighting, autocomplete, and validation.
Query Templates
DNS, Recon, Threat, Security, WHOIS, BGP, and more.
Export Anywhere
Table, graph view, raw JSON, CSV. Copy or pipe to tools.
Templates
Pre-built templates for common investigations
Don’t want to write queries? Start from a template. One click gives you a ready-to-run investigation for any of these categories.
- →Find Subdomains — all subdomains of a domain
- →CNAME Chain — follow alias chain up to 5 hops
- →Reverse DNS — all hostnames resolving to an IP
- →Find Nameservers — nameservers for a domain
- →Suffix Domain Search — FST-indexed hostname search
- →NS + MX Combined — nameservers and mail servers
AI Context
Your AI agent, with full
infrastructure context
Whisper is the first infrastructure intelligence platform with native MCP support. Connect Claude, GPT, Gemini, or any MCP-compatible agent and give it the ability to answer questions about internet infrastructure that no LLM can answer on its own. Connect in under a minute and start querying.
{ "mcpServers": { "whisper": { "url": "https://mcp.whisper.security/sse", "headers": { "Authorization": "Bearer YOUR_API_KEY" } } } }
Investigate suspicious-domain.xyz — who is behind it and what infrastructure do they control?
Using whisper_graph_query…
suspicious-domain.xyz resolves to 185.234.xx.xx, which belongs to AS399629 (BL Networks, known bulletproof hosting). This IP co-hosts 47 other domains, including 12 flagged by threat feeds. The same registrant email appears on 23 domains across 3 different ASNs. WhisperRank threat score: 94/100 (structural risk: bulletproof hosting neighborhood).
Full report with evidence chain attached.
We’re actively building AI Context into a full service — expanding what agents can do with infrastructure intelligence. More soon.
Data sources
What’s in the graph
18 data source types, continuously ingested and correlated. Every layer of internet infrastructure, from routing tables to certificates.
Use cases
What you can do with it
Enrich every alert automatically
Any IP or domain that triggers an alert gets instant infrastructure context. Who owns it, what it connects to, how risky it is, what else shares its infrastructure. Integrates directly into Splunk, Sentinel, and your SOAR playbooks.
Investigate threats end-to-end
Trace adversary infrastructure across DNS, BGP, hosting, WHOIS, and certificate layers. Starting from 2 OFAC-designated domains, Whisper identified 60+ connected domains and uncovered an entire cluster of businesses sharing infrastructure.
Discover your full attack surface
Map every asset connected to your organization — including shadow IT, forgotten subdomains, shared hosting relationships, and infrastructure dependencies no scanner can see.
Detect phishing infrastructure as it forms
Spot brand impersonation the moment a lookalike domain is registered. Track certificate issuance, DNS changes, and hosting patterns continuously.
Hunt proactively for threats
Search for suspicious infrastructure patterns before they become incidents. Whisper detected an active Iranian APT campaign (Prince of Persia) and found a live C2 server that was not in any public threat feed.
AI-assisted investigation reports
Ask your AI agent to investigate a domain. Whisper provides the infrastructure context via MCP. The agent writes a full report with ownership, hosting, risk scoring, and historical changes — in seconds.
See what your current tools can’t see
Get a live demo with your own infrastructure data. Technical POC in days, not months.